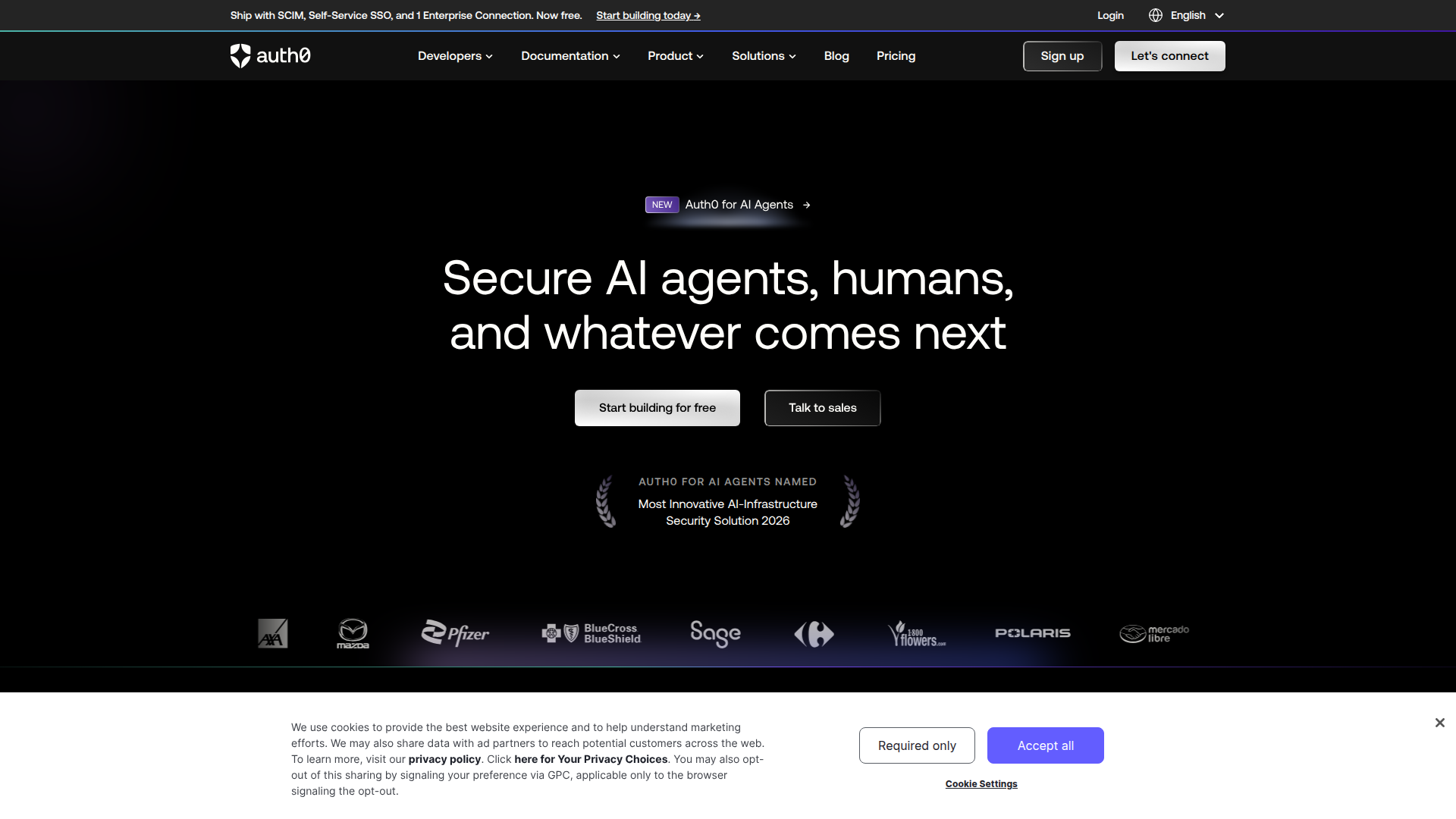
Auth0
Connect Auth0, an identity and access management platform, with Webflow to add login, signup, and content gating to static sites through the SPA SDK, Lock widget, automation platforms, or direct API integration.

Webflow handles design and publishing well. What it does not include is server-side authentication, session management, or user identity handling. If a site needs login functionality, gated content, or role-based access, that logic has to come from somewhere else. Webflow's native User Accounts feature is also being discontinued by January 29, 2026, which makes third-party authentication a requirement for any new project.
Connecting Auth0 with Webflow gives static sites a full identity layer. Auth0 handles user registration, social login, multi-factor authentication, and JWT-based session management. Webflow remains the presentation layer. Users authenticate through Auth0's hosted login page or an embedded widget. Custom JavaScript on the Webflow side reads the resulting token to control what content appears. Auth0 Actions can also write user data directly to the Webflow CMS API on signup, keeping member directories or profile pages in sync automatically.
This integration is most relevant to developers building membership sites, SaaS founders adding customer portals, and agencies delivering client projects that need enterprise SSO, SAML federation, or social login without standing up a full backend.
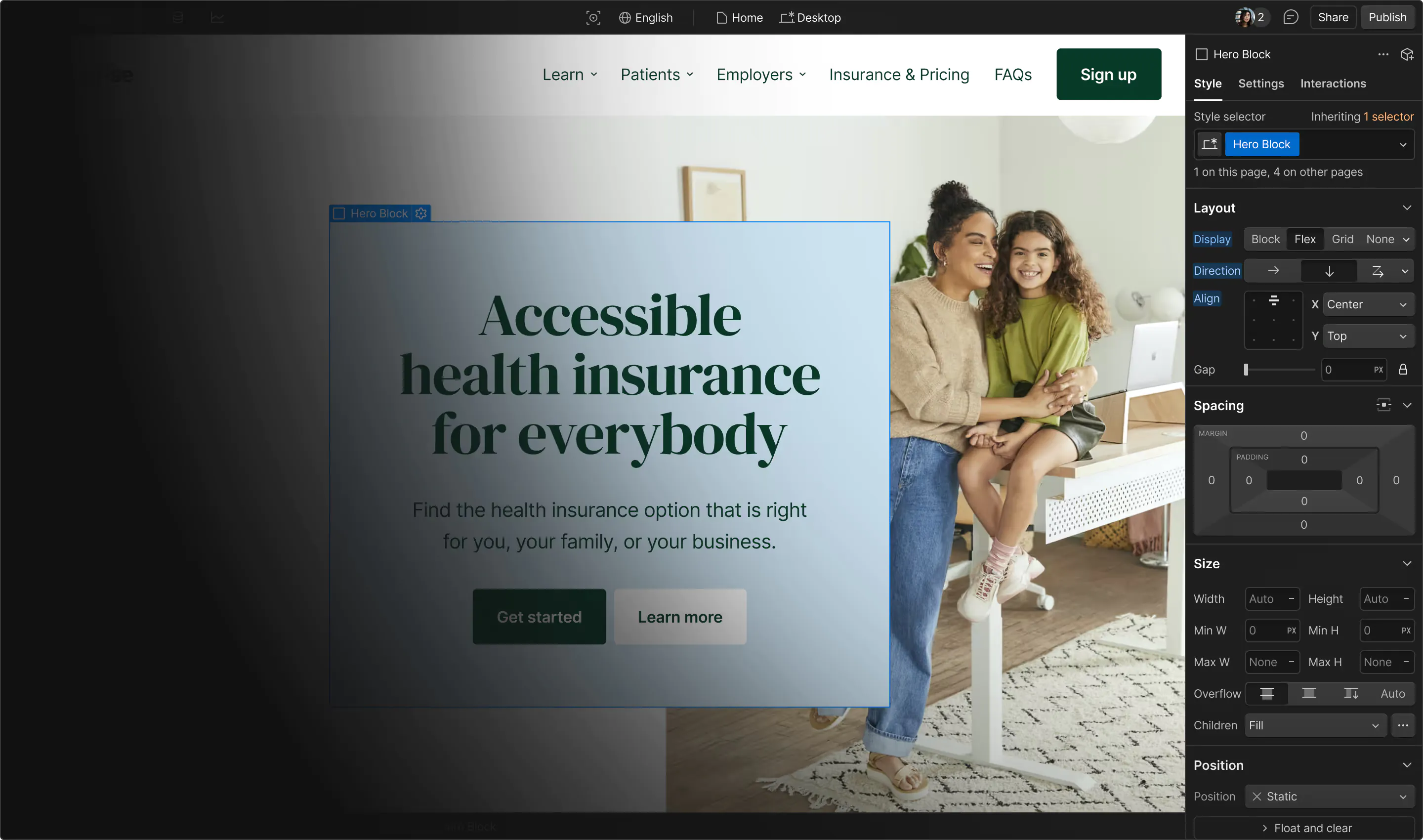
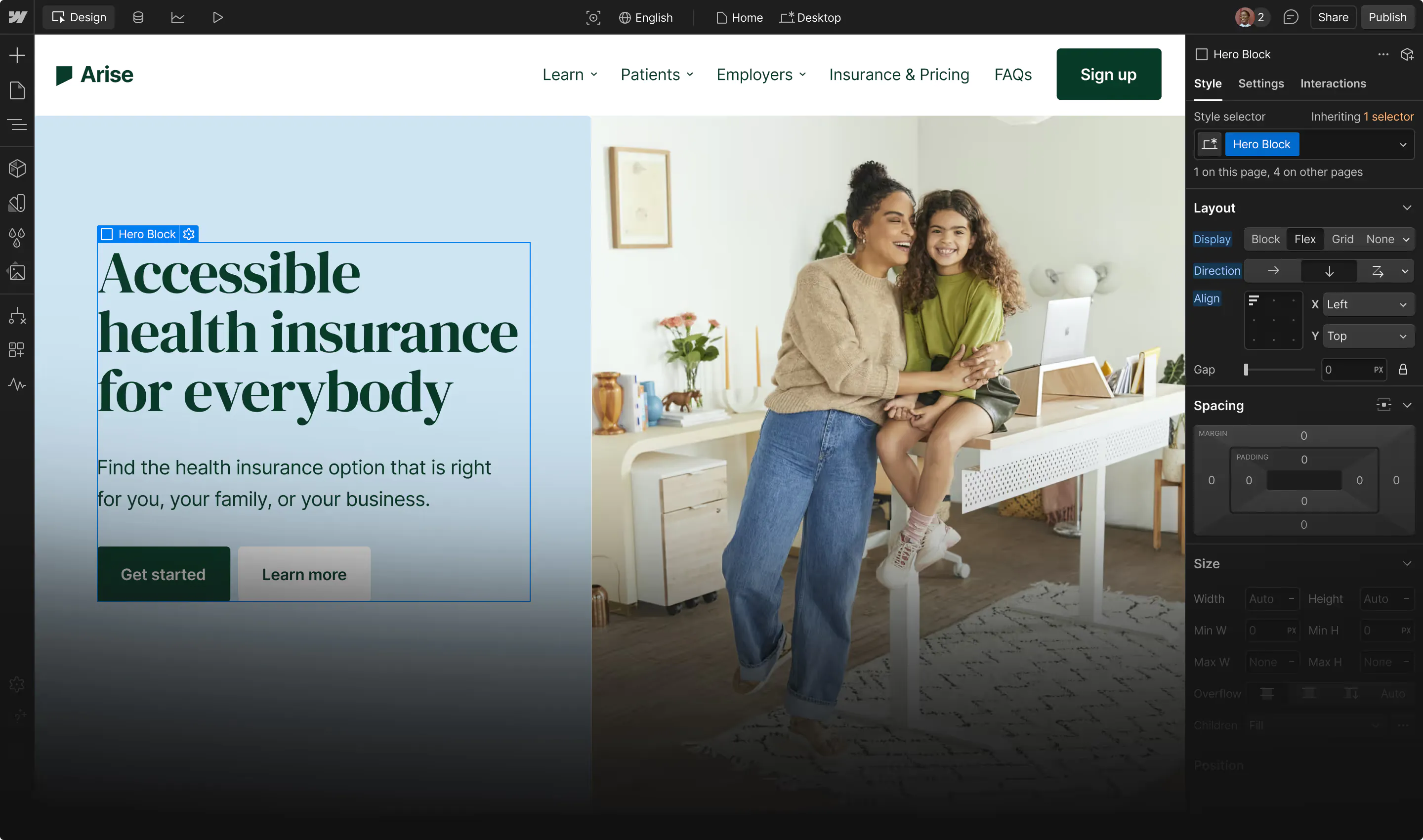
How to integrate Auth0 with Webflow
What is Auth0? Auth0 is an identity and access management platform from Okta. It provides authentication, authorization, social login, multi-factor authentication, and user management through hosted login pages, SDKs, and REST APIs. Auth0 supports 30+ SDKs and quickstart guides covering JavaScript, React, iOS, Android, and more.
Auth0 does not have a native app on the Webflow Marketplace, so integration relies on custom code, automation platforms, or direct API calls. The integration supports four approaches:
- The Auth0 SPA SDK via custom code redirects users to Auth0's Universal Login page and handles authentication entirely in the browser, with no build tools required.
- The Auth0 Lock widget via a Code Embed element places an inline login form directly on a Webflow page for modal-style or dedicated login flows.
- Automation platforms — Make, n8n, or viaSocket — sync Auth0 user events to the Webflow CMS without writing code.
- The Auth0 and Webflow APIs support server-side user sync, role-based access control, and subscription gating, but require a serverless function layer.
Most production implementations combine at least two of these methods — typically the SPA SDK for front-end authentication plus an automation platform or API integration for CMS data sync.
Add Auth0 authentication with the SPA SDK
The most common approach loads Auth0's SPA SDK onto a Webflow site and redirects users to Auth0's Universal Login page. This method works with Webflow's static hosting and requires no build tools. Auth0 recommends the Authorization Code Flow with PKCE for browser-based apps. The Vanilla JS SPA Quickstart provides the closest official reference for Webflow implementations. The SDK loads from a CDN and runs entirely in the browser.
To set up the integration:
- Load the SDK by adding a
<script>tag to custom code in your site's head tag via Site settings > Custom Code > Head code:
<script src="https://cdn.auth0.com/js/auth0-spa-js/2.0/auth0-spa-js.production.js"></script>
- Check the Auth0 SPA SDK releases page for the latest patch version before publishing.
- Create a Single Page Application in the Auth0 Dashboard, then register your Webflow domain in Allowed Callback URLs, Allowed Logout URLs, and Allowed Web Origins — missing any one field causes authentication failures.
- Register both your staging domain (
https://yoursite.webflow.io) and production domain (https://yourdomain.com) in all three fields. - Create a
/callbackpage in Webflow's Pages panel to handle the redirect after login. - Add login and logout JavaScript to Site settings > Custom Code > Footer code using
loginWithRedirect(),handleRedirectCallback(), andisAuthenticated()from the SPA SDK reference. - Use
getAccessTokenSilently()on each page load to maintain sessions across multiple Webflow pages without requiring re-login.
JavaScript added through custom code does not execute in Webflow's canvas preview — publish the site and test on the live URL. For multi-page Webflow sites, in-memory token storage means tokens are lost on page refresh. The SDK's silent authentication re-acquires tokens automatically, depending on the correct Allowed Web Origins configuration. This can fail in browsers that block third-party cookies (Safari ITP, Firefox ETP). Enabling useRefreshTokens: true in the SDK config provides a fallback.
Embed the Auth0 Lock widget with a Code Embed element
Auth0's Lock widget renders an inline login form directly on a Webflow page using a Code Embed element. Users log in without leaving the page. This works well for modal-style sign-in flows or dedicated login pages.
To set up the Lock widget:
- Add a Code Embed element to your page from the Add panel, then paste the Lock library script and initialization code, specifying your Client ID, Auth0 domain, and a container ID for the target
<div>. - Configure display options through the Lock API —
allowLogin,allowSignUp,initialScreen, andprefillparameters control which screens and fields appear. - Set
auth.redirectUrlto your Webflow callback page andresponseTypetotoken id_token.
Auth0 recommends Universal Login (the redirect-based SPA SDK method) over the embedded Lock widget for new implementations. Embedded login uses cross-origin authentication, which depends on third-party cookies that modern browsers increasingly block by default. Without a custom domain configured on Auth0, expect authentication issues in Safari and Firefox. The Code Embed element supports up to 50,000 characters per block, which is sufficient for Lock initialization code. Lock is a viable choice for inline forms, but is generally a secondary option.
Connect with Make, n8n, or viaSocket
Automation platforms connect Auth0 user events to Webflow CMS actions without writing code. This is the most accessible path for syncing user data, creating member records on signup, updating profiles on changes, or removing CMS items when users are deleted. Make provides the most complete Auth0 + Webflow connector, with both triggers and actions for each service.
- Make's Auth0 module includes a Watch Users trigger (fires on new user creation) plus Create a User, Delete a User, Update a User, Search Users, and Search Users by Email actions.
- Make's Webflow module includes Create an Item, Create a Live Item, Update an Item, Update a Live Item, Delete an Item, and Find Live Item actions, among others.
- n8n accesses Auth0 via HTTP Request nodes (supporting all Management API v2 endpoints) and connects to Webflow through a native node with Create, Delete, Get, and Update operations.
- viaSocket provides Webflow triggers (New Form Submission, Site Published, Page Created) paired with an Auth0 Get User action. Note that viaSocket currently offers no Auth0 triggers, though its connector catalog changes frequently — confirm availability before building a workflow that depends on it.
For most no-code use cases, Make is the recommended platform because it is the only one offering both an Auth0 trigger and Webflow live item publishing in a single workflow.
Sync new Auth0 users to the Webflow CMS
The most common automation creates a Webflow CMS item whenever a new user registers in Auth0. On Make, this uses the Watch Users trigger connected to a Create a Live Item action. The workflow maps Auth0 user fields (name, email, user ID) to CMS collection fields, and the new record publishes immediately. This pattern works for member directories, team pages, or user profile listings. On n8n, the same flow uses an HTTP Request node to interact with Auth0's Management API, paired with Webflow's native Create operation.
To configure this sync:
- Map
user_idfrom Auth0 to a dedicatedauth0-user-idtext field in the Webflow CMS collection — this field is required for all subsequent update and lookup operations. - Use Create a Live Item (not Create an Item) if the record should appear on the published site immediately.
- For social login users, note that the
user_idformat follows the patterngoogle-oauth2|1234567890, which differs from database connection IDs.
Webflow's CMS plan supports up to 2,000 items, and the Business plan supports up to 10,000 items, so factor collection size limits into directory-style implementations.
Update or remove CMS records on user changes
Make and n8n also handle ongoing sync when user profiles change, or accounts are deleted. On Make, an Auth0 webhook trigger detecting user updates drives a Webflow Update Live Item action. For deletions, the trigger fires a Webflow Delete an Item action that removes the corresponding CMS record.
- Use Make's Search Users by Email or n8n's
GET /api/v2/usersto find the Auth0 user, then pass the mapped Webflow item ID to the Update or Delete action. - Schedule periodic reconciliation workflows to catch any events missed during downtime.
These automation flows run outside Webflow's hosting, so they are not affected by Webflow's static-site limitations or CORS restrictions.
Build with the Webflow and Auth0 APIs
For implementations that need server-side token validation, JWT custom claims, or programmatic CMS writes, the Auth0 Management API and Webflow Data API v2 provide full control. This approach requires a serverless function layer (Cloudflare Workers, AWS Lambda, Vercel Edge Functions, or Webflow Cloud). Auth0 Management API tokens and Webflow API tokens must never appear in client-side code. The Auth0 Authentication API reference and Webflow API v2 reference document all available endpoints.
- The Auth0 SPA SDK handles browser-side authentication via
GET /authorizeandPOST /oauth/tokenusing the Authorization Code Flow with PKCE. - Auth0 Actions run server-side on specific triggers (
post-user-registration,post-login,post-change-password) and can call the Webflow API directly using secrets stored in the Action configuration. - The Webflow Data API v2 supports creating, reading, updating, and deleting CMS items at endpoints like
POST /v2/collections/{collection_id}/itemsandPATCH /v2/collections/{collection_id}/items/{item_id}. - Auth0's Management API v2 at
https://{domain}/api/v2/provides user CRUD operations, role assignment, and metadata updates, all requiring a Bearer token with the appropriate scopes.
All Webflow CMS API calls from Auth0-authenticated contexts must route through a server-side intermediary. Browser-based calls to the Webflow API fail with CORS errors in production.
Sync users to the Webflow CMS with Auth0 Actions
Auth0 Actions run custom JavaScript on identity events and can write directly to the Webflow CMS API. The post-user-registration trigger fires after a new database or passwordless user is created, making it the right hook for creating CMS member records on signup. Store the Webflow API token and collection ID as Action Secrets — never hardcode them.
To configure this sync:
- Note that the
post-user-registrationtrigger fires asynchronously and only for database and passwordless connections. It does not fire for social or enterprise logins. - For social login users, use the
post-logintrigger with anevent.stats.logins_count === 1check to detect first-time logins and create the CMS record then. - The
post-change-passwordtrigger is observational only (noapiobject) but can call the Webflow API to update alast-password-changefield on the corresponding CMS item. - Auth0 Actions do not include a user-deleted trigger. Detecting deletions requires configuring a Log Stream webhook that filters for the
sdu(Success User Deletion) event code.
Auth0 Rules and Hooks are both deprecated and will stop executing on November 18, 2026. All new implementations should use Actions exclusively.
Gate content with JWT custom claims
Auth0 Actions can inject custom claims into JWTs at login time, and client-side JavaScript on the Webflow site reads those claims to show or hide content. This pattern works for subscription tiers, role-based access, or course enrollment checks.
- In a
post-loginAction, callapi.accessToken.setCustomClaim()to add a namespaced claim likehttps://myapp.com/subscription_tierwith a value read fromevent.user.app_metadata. - On the Webflow side, call
getTokenSilently()from the SPA SDK, decode the JWT, and check the custom claim value before toggling CSS visibility on gated page sections. - Assign roles to users via
POST /api/v2/users/{id}/roles(requirescreate:role_membersscope), then injectevent.authorization.rolesinto the JWT for client-side role checks. - Verify JWTs server-side using the public keys at
GET /.well-known/jwks.jsonbefore returning protected data from any API endpoint.
Client-side content gating with CSS visibility is a UX convenience, not a security boundary. Any content delivered to the browser is accessible to determined users. For true access control, validate tokens server-side before returning protected content from an API.
Manage subscriptions with Stripe, Auth0, and Webflow
A common three-service architecture uses Stripe for payments, Auth0 for identity, and Webflow for the front end. Stripe webhook events update Auth0 user metadata, which then flows into JWT custom claims and Webflow CMS records.
- A serverless function receives Stripe webhook events (like
subscription.updated), verifies the webhook signature, and callsPATCH /api/v2/users/{id}on the Auth0 Management API to updateapp_metadatawithsubscription_activeandplanvalues. - On the next login, a
post-loginAction readsevent.user.app_metadata.subscription_activeand injects it as a JWT custom claim. - The same serverless function can call
PATCH /v2/collections/{collection_id}/items/{item_id}on the Webflow Data API to update the member's CMS record with their current subscription status. - Look up the Auth0 user from a Stripe customer ID using
GET /api/v2/users?q=app_metadata.stripe_customer_id:{cus_id}&search_engine=v3.
M2M tokens are required for all server-side Auth0 Management API calls. Cache tokens for their full expires_in duration to avoid unnecessary token requests. This architecture separates billing, identity, and presentation cleanly while keeping each system in its strongest role.
What you can build with the Auth0 Webflow integration
Integrating Auth0 with Webflow lets you add production-grade authentication and access control to static sites without building a custom backend.
Here are a few things you can build with this integration:
- Gated membership site with subscription billing: Connect Auth0 login to a Stripe webhook handler that updates
app_metadata; apost-loginAction injects subscription status as a JWT claim that client-side JavaScript reads to show premium content only to paying subscribers. - E-learning platform with course-level access: Use Auth0 JWTs carrying custom claims that encode course access; a serverless function validates tokens before returning signed Vimeo URLs, so only enrolled students reach video playback.
- Auto-populated member directory: Sync new Auth0 registrations to a Webflow CMS collection using Make's Watch Users trigger and Create a Live Item action; each signup publishes a profile page displayed in a Collection List on the site automatically.
- B2B customer portal with enterprise SSO: Use Auth0 Organizations to give each enterprise client its own SAML-federated login, per-tenant branding, and role assignments without managing separate authentication systems.
For simpler implementations, start with the SPA SDK method for front-end authentication and a Make workflow for CMS sync. For enterprise requirements like RBAC, multi-tenancy, or subscription gating, add Auth0 Actions and the Webflow Data API.
Frequently asked questions
Yes. Auth0's SPA SDK runs entirely in the browser and requires no server-side runtime. Webflow serves the static HTML, CSS, and JavaScript files, and the SDK handles authentication through redirects to Auth0's hosted login page. The Vanilla JS SPA Quickstart is the closest official reference for this setup. Server-side token validation, Management API calls, and Webflow API writes require a separate serverless function layer in Cloudflare Workers, AWS Lambda, or Webflow Cloud because API tokens must never appear in client-side code.
Use the Authorization Code Flow with PKCE. Auth0 recommends this flow for single-page applications and static sites. It mitigates the risks of issuing tokens to public clients that cannot store secrets. The implicit grant flow (passing tokens in URL fragments) is not recommended for new implementations per Auth0's guidance.
Use Auth0 or another third-party provider for new projects. Webflow's native User Accounts feature is being discontinued by January 29, 2026. Auth0 supports social login, multi-factor authentication, role-based access control via custom JWT claims, and enterprise SSO — none of which Webflow Memberships offers. The tradeoff is that Auth0 requires custom JavaScript on the Webflow side, whereas Webflow Memberships was a no-code feature.
This is almost always a missing or incorrect Allowed Web Origins value in the Auth0 Application settings. The SPA SDK uses silent authentication via a hidden iframe to check Auth0's session cookie on page load. If the Webflow domain is not listed in Allowed Web Origins, this check fails and the user appears logged out. Confirm your exact domain (including
https://) appears in this field for both staging and production URLs. Browsers that block third-party cookies (Safari, Firefox) can also cause silent authentication to fail even with correct configuration — enableuseRefreshTokens: truein the SPA SDK configuration as a fallback.Yes. Webflow's developer documentation lists Auth0 as a supported authentication provider for Webflow Cloud's edge/serverless environment. Use the
joselibrary for JWT verification (notjsonwebtoken, which requires Node.js APIs unavailable at the edge), and usefetchfor all HTTP requests. Avoid using NextAuth.js as an Auth0 wrapper in Webflow Cloud. It depends on Node.js-specific modules that are not compatible with the edge runtime.

Description
Auth0 adds authentication, social login, MFA, and JWT-based access control to Webflow sites through custom code, automation platforms, or direct API integration.
This integration page is provided for informational and convenience purposes only.
Anthropic Claude
Webflow's Model Context Protocol (MCP) server connects Claude AI directly to your site's CMS, Designer APIs, and data layer.
ChatGPT
Direct API integration provides complete control over AI functionality compared to pre-built solutions, enabling custom conversation flows, context management, and advanced processing patterns that aren't possible through standard embeds.

Xano
Connect your Webflow site to a powerful no-code backend platform that handles databases, APIs, and business logic — all without writing server-side code.

Zapier
Connect Zapier's powerful automation platform with Webflow to streamline workflows, sync data across 8,000+ apps, and eliminate manual tasks. Transform your website into an automated hub that captures leads, processes orders, and updates content without writing code.
ScheduleFlow
Connect ScheduleFlow to Webflow to schedule site and CMS publishes at specific dates and times.
Neon
Connect Neon, a serverless Postgres database, with Webflow to store, query, and sync relational data that exceeds what the Webflow CMS supports natively.
Slater
Connect Slater with Webflow to write, test, and deploy custom JavaScript through an AI-assisted editor with staging environments and version history — without a full site publish for every change.
Relay.app
Connect Relay.app with Webflow to automate form processing, CMS updates, and e-commerce order management using workflows with AI steps and human approval checkpoints.
Sass
Write and compile Sass directly in Webflow with live preview, code autocompletion, and minified CSS output using the free Sass app.