Understanding and addressing common cyberthreats can safeguard sensitive data, uphold your brand’s reputation, and reduce costs.
The booming rise of ecommerce and digital business platforms brings both opportunities and vulnerabilities. As online businesses grew in 2022, cyberattacks rose 38% from 2021, underscoring the importance of strong digital security. By adopting the right strategies, you cultivate a safer environment, allowing your website — and brand — to thrive without the looming shadow of cyberthreats.
What is website security?
Website security encompasses comprehensive measures and best practices to protect websites from unauthorized access, data breaches, and cyberattacks. Strong website security measures ensure that sensitive data, such as personal customer details and financial information, remain encrypted and inaccessible to malicious actors. This fosters trust, assuring users that their information is safe on your website. A secure website also upholds a brand’s reputation by demonstrating a commitment to user privacy and protection.
6 common website security threats and how to combat them
The first step to preventing cyber attacks is identifying common threats. Here are a few potential dangers to your site — and strategies to tackle them.
1. Malware
Malware, short for malicious software, describes harmful programs that infiltrate and damage computer systems, including websites. Malware can disrupt regular functionality, steal sensitive data, or take control of core operations, such as admin access. Viruses, ransomware, and spyware are all examples of malware.
How to protect your website from malware
- Regularly update and patch software and plugins. Malware targets preexisting security loopholes in software and plugins. Regular updates and patches fix these flaws, making it harder for hackers to break in. Using vetted plugins and apps from trusted developers, such as Apps available on Webflow, also protects against outdated software with security vulnerabilities.
- Install a reputable antivirus solution. Installing an antivirus or anti-malware solution on your server or hosting environment adds extra protection. These programs actively scan and monitor files, databases, and incoming traffic for suspicious patterns or known malware signatures. When they identify potential threats, the software neutralizes them before they can exploit vulnerabilities in your website.
- Deploy a web application firewall (WAF). A WAF acts as a shield by analyzing incoming site traffic, filtering out unwanted visitors, and thwarting common web attacks. By identifying attack patterns such as structured query language (SQL) injections, which exploit input fields, and cross-site scripting that embeds malicious scripts into a site’s underlying code, WAF prevents harmful requests from reaching your site.
- Perform routine security scans and audits. Regularly scanning your website and troubleshooting website security issues helps you fix system flaws before hackers exploit them, allowing you to pivot quickly and improve existing security measures.
- Educate your team about safe online behavior. Host awareness training workshops to educate team members about safe online practices, such as downloading or clicking on suspicious links. This is a cost-effective way to improve your website’s security and reduce the likelihood of both human error and novice mistakes.
2. Data breach
A data breach occurs when cybercriminals gain unauthorized access to sensitive and confidential data, potentially leading to significant legal, financial, and reputational losses.
How to protect your website from a data breach
- Implement strong access controls and authentication mechanisms. Robust controls allow only authorized users to access data. Enforcing strict authentication mechanisms, such as robust passwords and two-factor authentication (2FA), lowers data exposure and breach risks by limiting potential entry points.
- Encrypt sensitive data during transmission and at rest. Attackers can’t read encrypted data, even if they intercept or steal it, rendering it useless. Be sure to encrypt data during transmission and at rest (in server or database storage) using ciphertext or private keys that only password holders can access.
- Comply with relevant data protection regulations. Data protection laws — such as the European Union’s GDPR (General Data Protection Regulation) and HIPAA (Health Insurance Portability and Accountability Act) in the US — set stringent standards for the handling and storing of sensitive information like healthcare records and personal data. By enforcing best practices for data management and imposing consequences for breaches, these regulations compel businesses to prioritize user privacy and data security. Adhering to these practices also strengthens users’ trust in your brand and helps you avoid the potential repercussions of noncompliance, such as heavy fines and reputational damage.
3. DoS and DDoS attacks
Denial-of-service (DoS) attacks overwhelm websites with excessive traffic, which renders them slow or inaccessible and disrupts user experiences. Distributed denial-of-service (DDoS) attacks originate from multiple sources and amplify the attack’s scale and complexity. While techniques combating DoS attacks often protect against DDoS attacks, DDoS attacks require more vigilant monitoring and advanced protective measures due to their distributed nature.
How to protect your website from attacks
- Use a content delivery network (CDN). CDNs allow you to spread data across servers in multiple locations. When a DoS or DDoS attack occurs, the distributed network shares the excessive load to reduce pressure on the main server. This way, users can still access your website during an attack.
- Adopt traffic filtering and set rate limits. Filtering identifies and blocks suspicious traffic sources to prevent attacks from overloading your site. Combined with rate limiting, which restricts the maximum number of requests users can make within a specific time frame, these measures ensure your site remains functional and resistant to DoS and DDoS attacks.
- Use load balancing to distribute traffic evenly. Like CDNs, load balancers distribute traffic across multiple servers, albeit in close geographical proximity. If a DoS or DDoS attack targets one server, the load balancer directs traffic away from the targeted server, allowing visitors to access your website, even under duress.
4. Ransomware
Ransomware is malware that blocks access to your data, holding it hostage by encrypting it until a victim, often the data owner or organization, pays a ransom — usually a cryptocurrency fee. Beyond the immediate demand for payment, these attacks can disrupt your business operations, damage your brand’s reputation, and potentially lead to permanent data loss if no backups exist.
How to protect your website against ransomware
- Regularly back up your website data and store backups offline. These backups act as insurance against ransomware. If attackers compromise and encrypt your data, offline stored copies provide a safe restoration point inaccessible to cybercriminals.
- Use strong passwords and consider multifactor authentication (MFA). Use strong, unique passwords with uppercase, lowercase, and special characters to add a layer of security to sensitive files. Doing so helps prevent brute force attacks — attempts by hackers to gain unauthorized access by systematically trying all possible password combinations — by making your password more challenging to guess. Implementing MFA further ensures that an additional verification step keeps unauthorized users out even if your password becomes compromised.
- Deploy endpoint security solutions. Endpoint security solutions are dedicated programs that identify and block ransomware attacks on individual systems. Installing multiple endpoint solutions on your devices can prevent ransomware-related crime and mitigate its impact.
5. Phishing schemes
Phishing schemes involve cybercriminals masquerading as legitimate businesses, organizations, or entities and using deception to obtain sensitive data, such as usernames and passwords.
How to protect your website from phishing
- Set up email filters and spam detectors. Phishing attacks often use email as a delivery mechanism. Protect users from phishing by setting up email filtering and spam detection tools to prevent deceptive messages, such as fake account notifications or unauthorized password reset requests, from reaching inboxes.
- Use domain validation and authentication techniques. Email authentication methods like SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) prevent unwanted actors from sending phishing emails by validating incoming emails, ensuring the sender is legitimate and genuine.
- Train your team members to recognize and validate email senders. Phishing emails disguise themselves by mimicking trusted sources, such as banks or company executives, but they often contain malicious links and attachments that endanger user data. Equip your team with the knowledge to verify sender authenticity, such as checking the email address, or use sender verification tools, like SPF or DMARC, to differentiate legitimate communications from phishing scams.
6. SQL injections
SQL injections occur when cybercriminals exploit flaws in a website’s input data by injecting malicious code through SQL queries, which allow them to access the site’s database.
How to secure your website against SQL injections
- Input validation and sanitization. Validating and sanitizing user input prevents hackers from inserting malicious code into your website’s database queries. You can filter harmful SQL commands and thwart injection attempts by authenticating input through data type checks, setting input length restrictions, and employing safelists, which only allow verified users to input data.
- Use parameterized queries or prepared statements. Parameterized queries and prepared statements use predefined SQL code and allow only specific data types as input to ensure that inserted data isn’t executable code. This separates user input from the SQL logic and prevents your website from mistakenly interpreting harmful inputs as part of SQL commands.
- Limit database user privileges. Limit user access by assigning roles and permissions. Setting specific access rights allows only authorized users to perform certain tasks or alter data entries. If an attacker attempts to exploit an SQL injection vulnerability, the system’s access controls prevent them from modifying sensitive data, keeping your information secure.
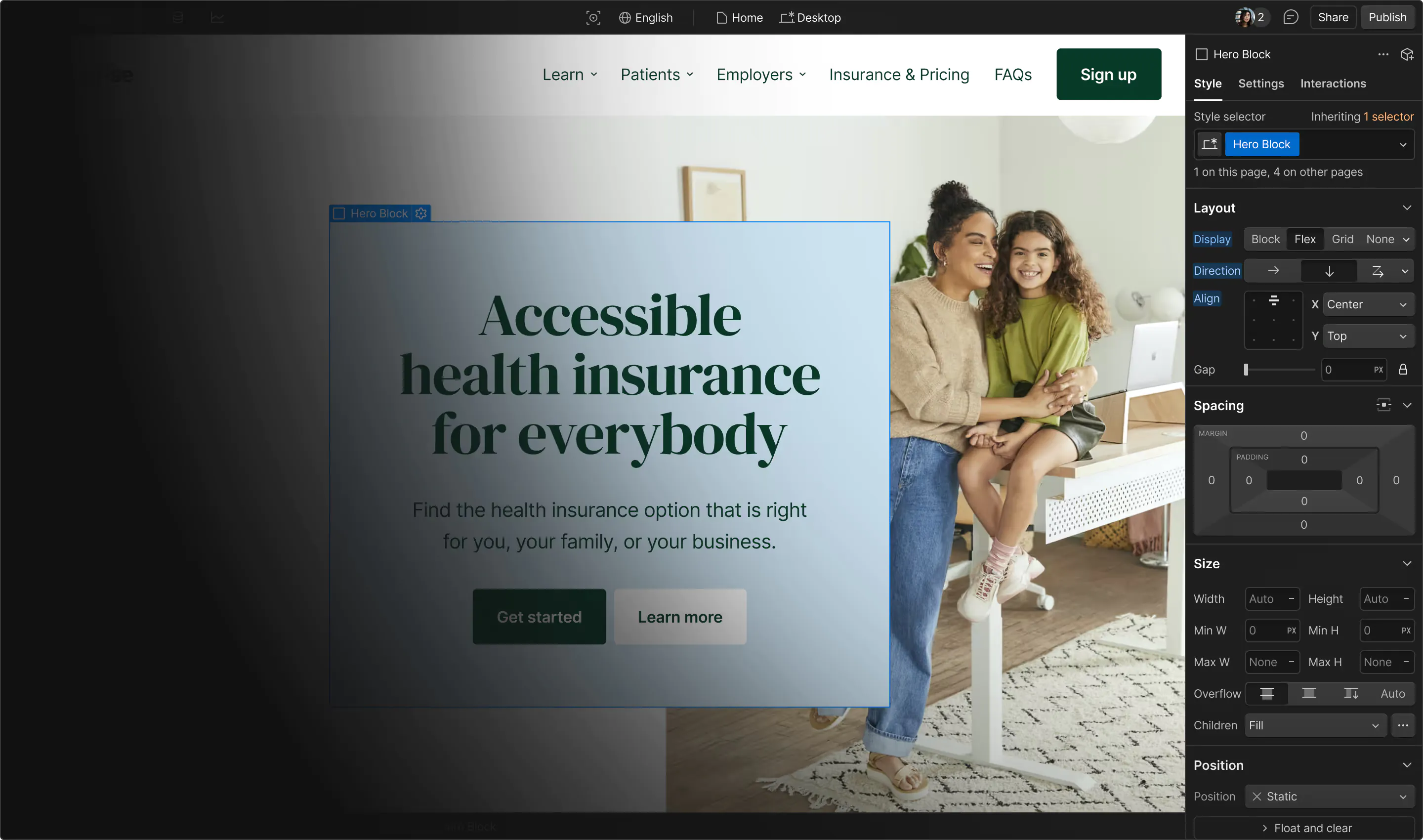
Safeguard your website with Webflow
Despite all these efforts, security and data breaches remain a potential risk. Whether you’re a small startup or an established enterprise, your website is home to all your content, products, and services, and protecting it against malicious practices is essential.
For peace of mind, Webflow builds security into your designs through HTTPS protocols and encrypted SSL certificates and hosting. To take your security even further, our in-depth security checklist also offers educational insights into web security basics and preventative measures to help keep your website safe.


















The marketer’s website
Our free ebook exclusively for marketers. Discover how no-code eliminates developer bottlenecks and empowers modern marketing teams to truly own the website.