Enterprise security is your first line of defense against digital threats.
As businesses shift from solely in-house servers to a complex combination of cloud platforms, third-party services, and dispersed teams, their security risks expand dramatically. While this new digital infrastructure increases efficiency and connectivity, it also introduces a variety of entry points for attackers to exploit, putting your business at risk for cybersecurity attacks and breaches. But with a solid understanding of enterprise security and risk management, you equip your team to actively confront and mitigate these vulnerabilities.
What’s enterprise security?
Enterprise security is the holistic strategy of safeguarding a company’s digital assets and sensitive data as it moves throughout your interconnected company network, transfers to off-site servers, and reaches end users. Beyond data, the practice extends to network security, shielding infrastructure — such as servers, databases, and cloud services — from breaches and intrusions. It also protects information assets, like confidential documents and proprietary software.
Moreover, enterprise security manages user access and identity verification, allowing only authorized personnel to access specific data sets or system functionalities. It further monitors potential internal threats by ensuring all employees maintain proper data-handling practices and comply with international standards and regulations, such as ISO/IEC 27001 and the European Union’s General Data Protection Regulation, or GDPR, to maintain system integrity and user trust.
Unlike traditional cybersecurity, which focuses on local or on-site data protection, enterprise security also extends its protective measures to cloud resources and mobile device management, recognizing and addressing the cloud-centric architectures common in today’s business environment.
By implementing comprehensive encryption methods, regular system audits, and real-time threat detection mechanisms, enterprise security ensures robust defense. This comprehensive approach underscores the company’s dedication to data privacy and security, reinforcing its reputation as a secure and reliable organization.
Why is enterprise security important?
As businesses increasingly extend operations beyond traditional in-house environments to cloud platforms like Amazon Web Services and other third-party solutions, they face heightened vulnerabilities. Such transitions put the onus of security on external vendors and can lead to protection gaps if not correctly managed. Historical incidents, like the breaches at Equifax and Target, highlight the severe consequences of these weaknesses: compromising the data of millions of users and eroding public trust in these brands.
Enterprise security addresses these concerns by securing data throughout its journey, ensuring a seamless and secure transition from internal networks to third-party platforms and end users.
Here are a few more benefits of implementing enterprise security.
Guard against cyberthreats
Cyberattacks, like data breaches and ransomware attacks, are becoming increasingly sophisticated and common.
These attacks don’t just threaten financial assets — they jeopardize a company’s reputation and compliance standing. A single breach can expose vital customer information, resulting in eroded trust, significant financial penalties, and potential legal ramifications. By actively identifying security flaws, implementing multilayered defense mechanisms, and actively monitoring for potential threats, enterprise security ensures that sensitive information remains inaccessible to unauthorized users.
Maintain team productivity
Cyberattacks not only jeopardize sensitive data but also risk damaging your company’s operational systems. When attackers deploy malicious software, essential platforms and tools, such as cloud storage and project management services, often are compromised, preventing teams from accessing vital resources. This interrupts daily workflows, hinders communication, and stalls essential tasks, leading to significant drops in productivity.
In addition, the aftermath of a cyberattack isn’t just about data recovery — it’s about time. Restoring systems and fortifying them against future threats demands attention and resources. This redirection pulls teams away from their core responsibilities and growth initiatives, further delaying projects and other strategic undertakings. Prioritizing enterprise security lets you proactively guard against these disruptions so you can maintain seamless operations and productivity.
Stay compliant
Enterprise security is key to staying compliant with data and privacy regulations. In recent years, governments and industry bodies have introduced a range of laws and standards to protect user data. These regulations include the European Union’s General Data Protection Regulation (GDPR), the U.S.’s Health Insurance Portability and Accountability Act (HIPAA), and the California Consumer Privacy Act (CCPA).
Falling short of these regulatory standards can lead to severe legal repercussions and hefty financial penalties. Beyond these tangible consequences, compliance underscores a company’s dedication to data protection. By proactively adhering to these standards, you not only avoid punitive actions but also communicate to your users that you’re committed to data privacy and security — and that commitment fosters brand loyalty and trust.
Build user trust
Users expect businesses to prioritize and secure their personal data. A lapse in security, such as a data breach, rapidly diminishes this trust, prompting customers to avoid platforms they deem unsafe. This disengagement doesn’t just influence immediate user behavior — it also risks tarnishing your website’s reputation, leading to reduced visibility on search engines. A clean security record not only maintains user loyalty but also boosts your site’s search engine optimization (SEO), keeping your brand trustworthy and discoverable online.


















No-code for enterprises
Our free ebook explains how no-code can help businesses scale. Learn how no-code can transform your company.
5 best practices for enterprise security
Since cyberattacks are becoming increasingly sophisticated, enterprise security best practices must evolve to match. Here are five essential enterprise security measures to consider.
1. Invest in organizational training
Prioritize regular training and awareness programs to empower your team with the knowledge and skills to detect and respond to threats. Incorporate interactive workshops, real-life scenario simulations, and continuous feedback to make training sessions more engaging and effective. As technology and threat landscapes evolve, consistent updates to these programs help keep your team ahead of emerging risks. A vigilant employee is often the difference between a thwarted attack and a security breach.
2. Secure data both at rest and in transit
For stored data, or data “at rest,” adding encryption provides a security layer that makes the information unreadable without the appropriate decryption key. When this data moves between systems — whether within your network, to off-site servers, or through third-party vendors — it becomes data “in transit.”
Using end-to-end encryption (E2EE) keeps your data secure throughout its journey. If unauthorized parties intercept this data, they’ll encounter encrypted, unintelligible content. This safeguards its integrity and confidentiality and emphasizes your dedication to maintaining the privacy and security of your data and users.
3. Monitor network performance
Constantly tracking and analyzing your network traffic lets you detect anomalous or suspicious activities. To monitor your traffic effectively, first establish a baseline of normal operations. This provides a reference point to measure and analyze real-time data flows. When this system detects deviations from the baseline, it signals a possible threat, allowing for quick interventions and security measures.
Given the continuous and complex nature of network traffic analysis, relying solely on manual oversight isn’t feasible (or recommended). Consider automating this process with tools or programs that offer consistent surveillance and rapid threat detection. Some website development platforms, like Webflow, integrate network traffic analysis as part of their security services, enhancing your security measures.
4. Manage endpoint access
Every connected device, whether a phone, laptop, or desktop computer, offers a potential entry point for threats. By employing endpoint security solutions such as intrusion detection systems, firewalls, and endpoint encryption tools, you minimize the risk of unauthorized access and data breaches. This proactive measure not only prevents unauthorized access but also minimizes the risk of data breaches. Regularly updating and reviewing access rights — combined with real-time monitoring — keeps your systems secure, even as your organization evolves.
5. Develop an enterprise security strategy
Creating a robust enterprise security strategy requires collaboration at all levels, especially with senior management. Their involvement ensures the strategy aligns with the organization’s objectives and secures necessary resources. Their endorsement also helps prioritize security initiatives, leading to timely implementation.
When top leaders actively support security measures, it resonates throughout the organization and fosters a culture where every team member values and practices good security habits.
Strategize enterprise security with risk management
As you configure your enterprise cybersecurity system, consider drawing upon risk management techniques to develop your plan. Risk management is the perfect complement to enterprise web security and actively enhances it by identifying, assessing, and addressing organizational threats. You can employ risk management for projects, products, or your operations.
One key aspect of risk management is risk assessment, which involves identifying potential hazards, analyzing the likelihood of them materializing, and anticipating the potential impact if they do. A clear understanding of these vulnerabilities lets you craft strategies to address them. Possible solutions include integrating encryption tools, setting robust access controls, or ensuring alignment with relevant industry standards and regulations.
While prevention is vital, preparedness is equally important. That’s where incident response planning comes into play within the risk management framework. Having a plan means you’re not just waiting for threats but are ready to act decisively from the moment you detect a breach to the aftermath, which may involve informing affected users.
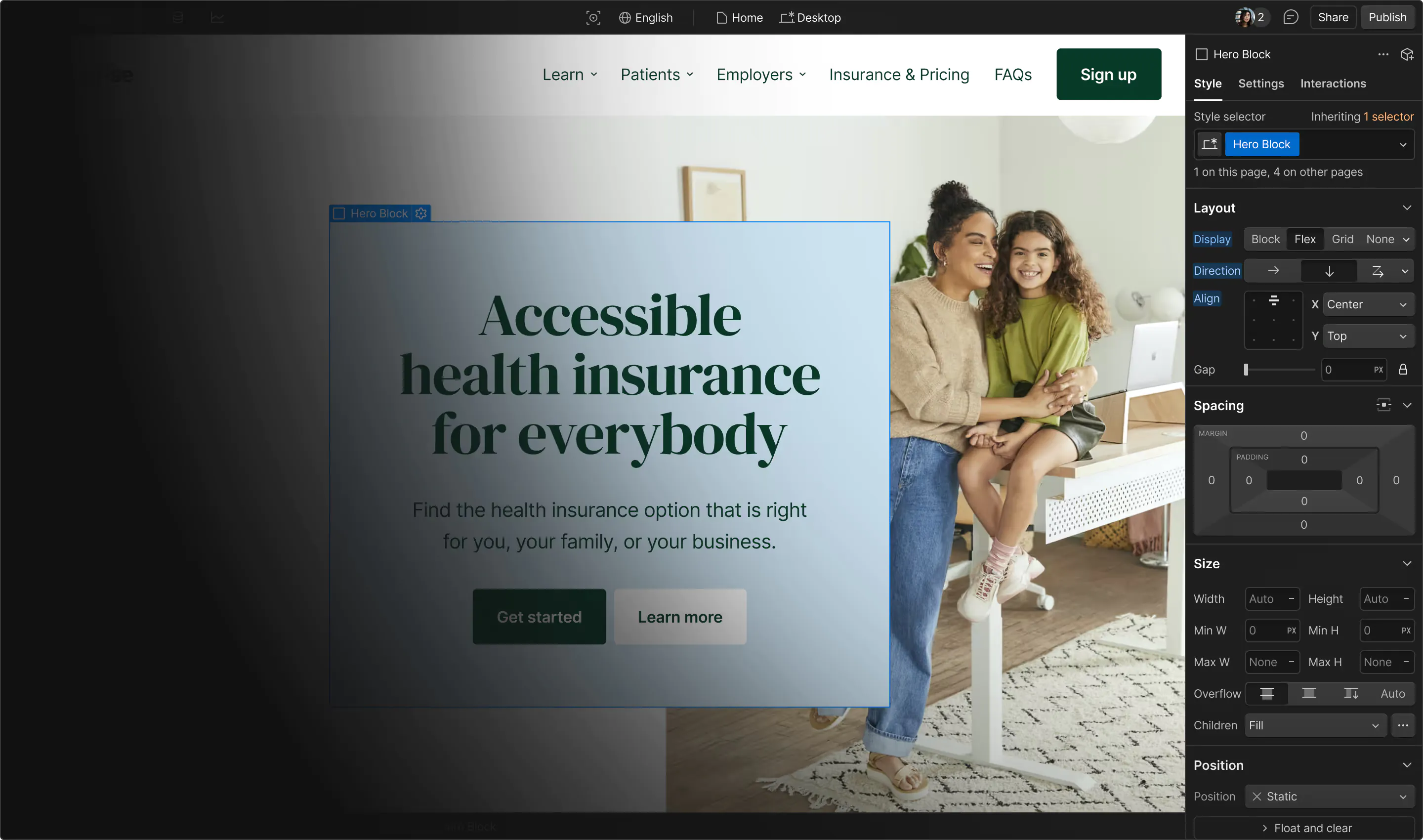
Build a secure enterprise platform with Webflow
If you’re not sure where to start building a secure enterprise-level platform, check out our security checklist. Or start with Webflow, a powerful visual web development platform that takes security to heart and builds it into its design. This way, you can spend more time on web design and creating features instead of worrying about site security.
Webflow Enterprise provides a robust and adaptable platform for creating secure enterprise websites and applications. Security features include enterprise data encryption, access controls, built-in SSL encryption, per-page password protection, single sign-on, SOC 2 Type II certification, enterprise network security protocols, advanced distributed denial-of-service (DDoS) protection, and more.